可以做书的网站公众号怎么引流推广
关于sr2t
sr2t是一款针对安全扫描报告的格式转换工具,全称为“Scanning reports to tabular”,该工具可以获取扫描工具的输出文件,并将文件数据转换为表格格式,例如CSV、XLSX或文本表格等,能够为广大研究人员提供一个可读的表格格式数据。

功能介绍
当前版本的sr2t支持处理下列工具生成的安全扫描报告:
1、Nmap (XML);
2、Nessus (XML);
3、Nikto (XML);
4、Dirble (XML);
5、Testssl (JSON);
6、Fortify (FPR);
工具依赖
1、argparse (dev-python/argparse);
2、prettytable (dev-python/prettytable);
3、python (dev-lang/python);
4、xlsxwriter (dev-python/xlsxwriter);
工具安装
由于该工具基于Python 3开发,因此我们首先需要在本地设备上安装并配置好最新版本的Python 3环境。
接下来,广大研究人员可以直接使用pip命令下载并安装sr2t:
pip install --user sr2t
或者使用下列命令将该项目源码直接克隆至本地:
git clone https://gitlab.com/0bs1d1an/sr2t.git
工具使用
我们可以通过一下两种方式来使用sr2t,如果我们以代码包的形式安装sr2t,则可以直接调用安装脚本:
sr2t --help
或者从项目目录调用工具脚本:
python -m src.sr2t --help
工具帮助信息
$ sr2t --helpusage: sr2t [-h] [--nessus NESSUS [NESSUS ...]] [--nmap NMAP [NMAP ...]][--nikto NIKTO [NIKTO ...]] [--dirble DIRBLE [DIRBLE ...]][--testssl TESTSSL [TESTSSL ...]][--fortify FORTIFY [FORTIFY ...]] [--nmap-state NMAP_STATE][--nmap-services] [--no-nessus-autoclassify][--nessus-autoclassify-file NESSUS_AUTOCLASSIFY_FILE][--nessus-tls-file NESSUS_TLS_FILE][--nessus-x509-file NESSUS_X509_FILE][--nessus-http-file NESSUS_HTTP_FILE][--nessus-smb-file NESSUS_SMB_FILE][--nessus-rdp-file NESSUS_RDP_FILE][--nessus-ssh-file NESSUS_SSH_FILE][--nessus-min-severity NESSUS_MIN_SEVERITY][--nessus-plugin-name-width NESSUS_PLUGIN_NAME_WIDTH][--nessus-sort-by NESSUS_SORT_BY][--nikto-description-width NIKTO_DESCRIPTION_WIDTH][--fortify-details] [--annotation-width ANNOTATION_WIDTH][-oC OUTPUT_CSV] [-oT OUTPUT_TXT] [-oX OUTPUT_XLSX][-oA OUTPUT_ALL]Converting scanning reports to a tabular formatoptional arguments:-h, --help 显示工具帮助信息和退出--nmap-state NMAP_STATE 指定过滤器的状态,例如open、filtered--nmap-services 指定服务补充列表--no-nessus-autoclassify 不对Nessus结果执行自动分类--nessus-autoclassify-file NESSUS_AUTOCLASSIFY_FILE指定覆盖一个自定义Nessus自动分类YAML文件--nessus-tls-file NESSUS_TLS_FILE指定覆盖一个自定义Nessus TLS YAML文件--nessus-x509-file NESSUS_X509_FILE指定覆盖一个自定义Nessus X.509 YAML文件--nessus-http-file NESSUS_HTTP_FILE指定覆盖一个自定义Nessus HTTP YAML文件--nessus-smb-file NESSUS_SMB_FILE指定覆盖一个自定义Nessus SMB YAML文件--nessus-rdp-file NESSUS_RDP_FILE指定覆盖一个自定义Nessus RDP YAML文件--nessus-ssh-file NESSUS_SSH_FILE指定覆盖一个自定义Nessus SSH YAML文件--nessus-min-severity NESSUS_MIN_SEVERITY指定输出的最低严重等级,例如1--nessus-plugin-name-width NESSUS_PLUGIN_NAME_WIDTH指定pluginid列的宽度,例如30--nessus-sort-by NESSUS_SORT_BY指定输出按照ip-address, port, plugin-id,plugin-name或severity排序--nikto-description-width NIKTO_DESCRIPTION_WIDTH指定description列的宽度,例如30--fortify-details 指定包含Fortify摘要、解释和针对每个漏洞的建议--annotation-width ANNOTATION_WIDTH指定annotation列的宽度,例如30-oC OUTPUT_CSV, --output-csv OUTPUT_CSV指定输出CSV名称,例如output-oT OUTPUT_TXT, --output-txt OUTPUT_TXT指定输出TXT文件,例如output.txt-oX OUTPUT_XLSX, --output-xlsx OUTPUT_XLSX指定输出XLSX文件,例如output.xlsx-oA OUTPUT_ALL, --output-all OUTPUT_ALL指定输出全部格式的输出基础文件名,例如outputspecify at least one:--nessus NESSUS [NESSUS ...]指定(多个)Nessus XML文件--nmap NMAP [NMAP ...]指定(多个)Nmap XML文件--nikto NIKTO [NIKTO ...]指定(多个)Nikto XML文件--dirble DIRBLE [DIRBLE ...]指定(多个)Dirble XML文件--testssl TESTSSL [TESTSSL ...]指定(多个)Testssl JSON文件--fortify FORTIFY [FORTIFY ...]指定(多个)HP Fortify FPR文件
工具使用样例
Nessus
$ sr2t --nessus example/nessus.nessus --no-nessus-autoclassify -oX example.xlsx


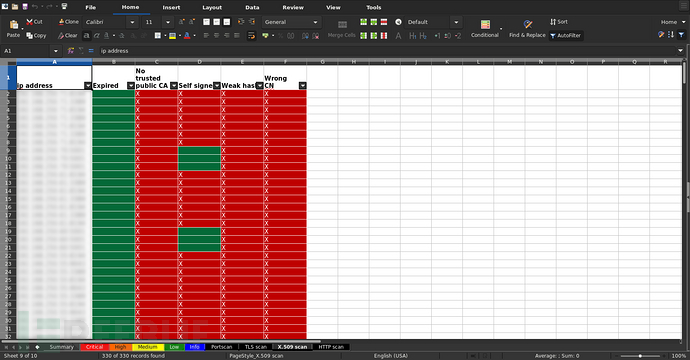
生成文本表格至stdout:
$ sr2t --nessus example/nessus.nessus+---------------+-------+-----------+-----------------------------------------------------------------------------+----------+-------------+| host | port | plugin id | plugin name | severity | annotations |+---------------+-------+-----------+-----------------------------------------------------------------------------+----------+-------------+| 192.168.142.4 | 3389 | 42873 | SSL Medium Strength Cipher Suites Supported (SWEET32) | 2 | X || 192.168.142.4 | 443 | 42873 | SSL Medium Strength Cipher Suites Supported (SWEET32) | 2 | X || 192.168.142.4 | 3389 | 18405 | Microsoft Windows Remote Desktop Protocol Server Man-in-the-Middle Weakness | 2 | X || 192.168.142.4 | 3389 | 30218 | Terminal Services Encryption Level is not FIPS-140 Compliant | 1 | X || 192.168.142.4 | 3389 | 57690 | Terminal Services Encryption Level is Medium or Low | 2 | X || 192.168.142.4 | 3389 | 58453 | Terminal Services Doesn't Use Network Level Authentication (NLA) Only | 2 | X || 192.168.142.4 | 3389 | 45411 | SSL Certificate with Wrong Hostname | 2 | X || 192.168.142.4 | 443 | 45411 | SSL Certificate with Wrong Hostname | 2 | X || 192.168.142.4 | 3389 | 35291 | SSL Certificate Signed Using Weak Hashing Algorithm | 2 | X || 192.168.142.4 | 3389 | 57582 | SSL Self-Signed Certificate | 2 | X || 192.168.142.4 | 3389 | 51192 | SSL Certificate Cannot Be Trusted | 2 | X || 192.168.142.2 | 3389 | 42873 | SSL Medium Strength Cipher Suites Supported (SWEET32) | 2 | X || 192.168.142.2 | 443 | 42873 | SSL Medium Strength Cipher Suites Supported (SWEET32) | 2 | X || 192.168.142.2 | 3389 | 18405 | Microsoft Windows Remote Desktop Protocol Server Man-in-the-Middle Weakness | 2 | X || 192.168.142.2 | 3389 | 30218 | Terminal Services Encryption Level is not FIPS-140 Compliant | 1 | X || 192.168.142.2 | 3389 | 57690 | Terminal Services Encryption Level is Medium or Low | 2 | X || 192.168.142.2 | 3389 | 58453 | Terminal Services Doesn't Use Network Level Authentication (NLA) Only | 2 | X || 192.168.142.2 | 3389 | 45411 | SSL Certificate with Wrong Hostname | 2 | X || 192.168.142.2 | 443 | 45411 | SSL Certificate with Wrong Hostname | 2 | X || 192.168.142.2 | 3389 | 35291 | SSL Certificate Signed Using Weak Hashing Algorithm | 2 | X || 192.168.142.2 | 3389 | 57582 | SSL Self-Signed Certificate | 2 | X || 192.168.142.2 | 3389 | 51192 | SSL Certificate Cannot Be Trusted | 2 | X || 192.168.142.2 | 445 | 57608 | SMB Signing not required | 2 | X |+---------------+-------+-----------+-----------------------------------------------------------------------------+----------+-------------+
输出至CSV文件:
$ sr2t --nessus example/nessus.nessus -oC example$ cat example_nessus.csvhost,port,plugin id,plugin name,severity,annotations192.168.142.4,3389,42873,SSL Medium Strength Cipher Suites Supported (SWEET32),2,X192.168.142.4,443,42873,SSL Medium Strength Cipher Suites Supported (SWEET32),2,X192.168.142.4,3389,18405,Microsoft Windows Remote Desktop Protocol Server Man-in-the-Middle Weakness,2,X192.168.142.4,3389,30218,Terminal Services Encryption Level is not FIPS-140 Compliant,1,X192.168.142.4,3389,57690,Terminal Services Encryption Level is Medium or Low,2,X192.168.142.4,3389,58453,Terminal Services Doesn't Use Network Level Authentication (NLA) Only,2,X192.168.142.4,3389,45411,SSL Certificate with Wrong Hostname,2,X192.168.142.4,443,45411,SSL Certificate with Wrong Hostname,2,X192.168.142.4,3389,35291,SSL Certificate Signed Using Weak Hashing Algorithm,2,X192.168.142.4,3389,57582,SSL Self-Signed Certificate,2,X192.168.142.4,3389,51192,SSL Certificate Cannot Be Trusted,2,X192.168.142.2,3389,42873,SSL Medium Strength Cipher Suites Supported (SWEET32),2,X192.168.142.2,443,42873,SSL Medium Strength Cipher Suites Supported (SWEET32),2,X192.168.142.2,3389,18405,Microsoft Windows Remote Desktop Protocol Server Man-in-the-Middle Weakness,2,X192.168.142.2,3389,30218,Terminal Services Encryption Level is not FIPS-140 Compliant,1,X192.168.142.2,3389,57690,Terminal Services Encryption Level is Medium or Low,2,X192.168.142.2,3389,58453,Terminal Services Doesn't Use Network Level Authentication (NLA) Only,2,X192.168.142.2,3389,45411,SSL Certificate with Wrong Hostname,2,X192.168.142.2,443,45411,SSL Certificate with Wrong Hostname,2,X192.168.142.2,3389,35291,SSL Certificate Signed Using Weak Hashing Algorithm,2,X192.168.142.2,3389,57582,SSL Self-Signed Certificate,2,X192.168.142.2,3389,51192,SSL Certificate Cannot Be Trusted,2,X192.168.142.2,445,57608,SMB Signing not required,2,X
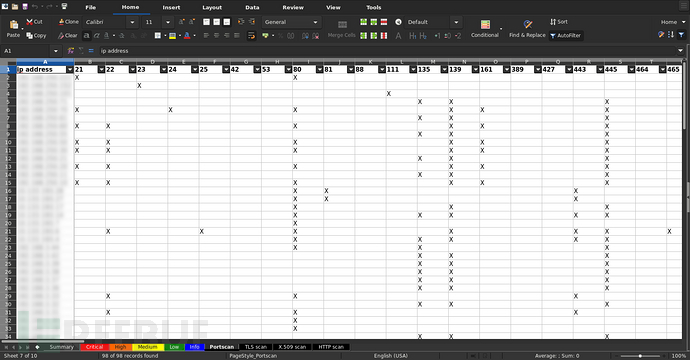
Nmap
$ sr2t --nmap example/nmap.xml -oX example.xlsx

生成文本表格至stdout:
$ sr2t --nmap example/nmap.xml --nmap-servicesNmap TCP:+-----------------+----+----+----+-----+-----+-----+-----+------+------+------+| | 53 | 80 | 88 | 135 | 139 | 389 | 445 | 3389 | 5800 | 5900 |+-----------------+----+----+----+-----+-----+-----+-----+------+------+------+| 192.168.23.78 | X | | X | X | X | X | X | X | | || 192.168.27.243 | | | | X | X | | X | X | X | X || 192.168.99.164 | | | | X | X | | X | X | X | X || 192.168.228.211 | | X | | | | | | | | || 192.168.171.74 | | | | X | X | | X | X | X | X |+-----------------+----+----+----+-----+-----+-----+-----+------+------+------+Nmap Services:+-----------------+------+-------+---------------+-------+| ip address | port | proto | service | state |+-----------------+------+-------+---------------+-------+| 192.168.23.78 | 53 | tcp | domain | open || 192.168.23.78 | 88 | tcp | kerberos-sec | open || 192.168.23.78 | 135 | tcp | msrpc | open || 192.168.23.78 | 139 | tcp | netbios-ssn | open || 192.168.23.78 | 389 | tcp | ldap | open || 192.168.23.78 | 445 | tcp | microsoft-ds | open || 192.168.23.78 | 3389 | tcp | ms-wbt-server | open || 192.168.27.243 | 135 | tcp | msrpc | open || 192.168.27.243 | 139 | tcp | netbios-ssn | open || 192.168.27.243 | 445 | tcp | microsoft-ds | open || 192.168.27.243 | 3389 | tcp | ms-wbt-server | open || 192.168.27.243 | 5800 | tcp | vnc-http | open || 192.168.27.243 | 5900 | tcp | vnc | open || 192.168.99.164 | 135 | tcp | msrpc | open || 192.168.99.164 | 139 | tcp | netbios-ssn | open || 192.168.99.164 | 445 | tcp | microsoft-ds | open || 192.168.99.164 | 3389 | tcp | ms-wbt-server | open || 192.168.99.164 | 5800 | tcp | vnc-http | open || 192.168.99.164 | 5900 | tcp | vnc | open || 192.168.228.211 | 80 | tcp | http | open || 192.168.171.74 | 135 | tcp | msrpc | open || 192.168.171.74 | 139 | tcp | netbios-ssn | open || 192.168.171.74 | 445 | tcp | microsoft-ds | open || 192.168.171.74 | 3389 | tcp | ms-wbt-server | open || 192.168.171.74 | 5800 | tcp | vnc-http | open || 192.168.171.74 | 5900 | tcp | vnc | open |+-----------------+------+-------+---------------+-------+
输出至CSV文件:
$ sr2t --nmap example/nmap.xml -oC example$ cat example_nmap_tcp.csvip address,53,80,88,135,139,389,445,3389,5800,5900192.168.23.78,X,,X,X,X,X,X,X,,192.168.27.243,,,,X,X,,X,X,X,X192.168.99.164,,,,X,X,,X,X,X,X192.168.228.211,,X,,,,,,,,192.168.171.74,,,,X,X,,X,X,X,X
Nikto
$ sr2t --nikto example/nikto.xml -oX example/nikto.xlsx

生成文本表格至stdout:
$ sr2t --nikto example/nikto.xml+----------------+-----------------+-------------+----------------------------------------------------------------------------------+-------------+| target ip | target hostname | target port | description | annotations |+----------------+-----------------+-------------+----------------------------------------------------------------------------------+-------------+| 192.168.178.10 | 192.168.178.10 | 80 | The anti-clickjacking X-Frame-Options header is not present. | X || 192.168.178.10 | 192.168.178.10 | 80 | The X-XSS-Protection header is not defined. This header can hint to the user | X || | | | agent to protect against some forms of XSS | || 192.168.178.10 | 192.168.178.10 | 80 | The X-Content-Type-Options header is not set. This could allow the user agent to | X || | | | render the content of the site in a different fashion to the MIME type | |+----------------+-----------------+-------------+----------------------------------------------------------------------------------+-------------+
输出至CSV文件:
$ sr2t --nikto example/nikto.xml -oC example$ cat example_nikto.csvtarget ip,target hostname,target port,description,annotations192.168.178.10,192.168.178.10,80,The anti-clickjacking X-Frame-Options header is not present.,X192.168.178.10,192.168.178.10,80,"The X-XSS-Protection header is not defined. This header can hint to the useragent to protect against some forms of XSS",X192.168.178.10,192.168.178.10,80,"The X-Content-Type-Options header is not set. This could allow the user agent torender the content of the site in a different fashion to the MIME type",X
Drible
$ sr2t --dirble example/dirble.xml -oX example.xlsx

生成文本表格至stdout:
$ sr2t --dirble example/dirble.xml+-----------------------------------+------+-------------+--------------+-------------+---------------------+--------------+-------------+| url | code | content len | is directory | is listable | found from listable | redirect url | annotations |+-----------------------------------+------+-------------+--------------+-------------+---------------------+--------------+-------------+| http://example.org/flv | 0 | 0 | false | false | false | | X || http://example.org/hire | 0 | 0 | false | false | false | | X || http://example.org/phpSQLiteAdmin | 0 | 0 | false | false | false | | X || http://example.org/print_order | 0 | 0 | false | false | false | | X || http://example.org/putty | 0 | 0 | false | false | false | | X || http://example.org/receipts | 0 | 0 | false | false | false | | X |+-----------------------------------+------+-------------+--------------+-------------+---------------------+--------------+-------------+
输出至CSV文件:
$ sr2t --dirble example/dirble.xml -oC example$ cat example_dirble.csvurl,code,content len,is directory,is listable,found from listable,redirect url,annotationshttp://example.org/flv,0,0,false,false,false,,Xhttp://example.org/hire,0,0,false,false,false,,Xhttp://example.org/phpSQLiteAdmin,0,0,false,false,false,,Xhttp://example.org/print_order,0,0,false,false,false,,Xhttp://example.org/putty,0,0,false,false,false,,Xhttp://example.org/receipts,0,0,false,false,false,,X
Testssl
$ sr2t --testssl example/testssl.json -oX example.xlsx
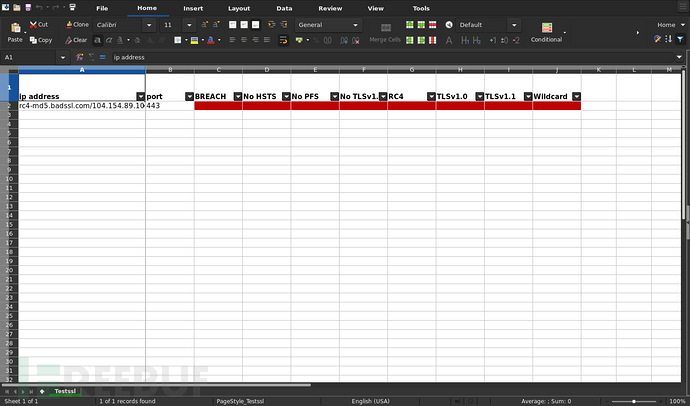
生成文本表格至stdout:
$ sr2t --testssl example/testssl.json+-----------------------------------+------+--------+---------+--------+------------+-----+---------+---------+----------+| ip address | port | BREACH | No HSTS | No PFS | No TLSv1.3 | RC4 | TLSv1.0 | TLSv1.1 | Wildcard |+-----------------------------------+------+--------+---------+--------+------------+-----+---------+---------+----------+| rc4-md5.badssl.com/104.154.89.105 | 443 | X | X | X | X | X | X | X | X |+-----------------------------------+------+--------+---------+--------+------------+-----+---------+---------+----------+
输出至CSV文件:
$ sr2t --testssl example/testssl.json -oC example$ cat example_testssl.csvip address,port,BREACH,No HSTS,No PFS,No TLSv1.3,RC4,TLSv1.0,TLSv1.1,Wildcardrc4-md5.badssl.com/104.154.89.105,443,X,X,X,X,X,X,X,X
Fortify
$ sr2t --fortify example/fortify.fpr -oX example.xlsx

生成文本表格至stdout:
$ sr2t --fortify example/fortify.fpr+--------------------------+-----------------------+-------------------------------+----------+------------+-------------+| | type | subtype | severity | confidence | annotations |+--------------------------+-----------------------+-------------------------------+----------+------------+-------------+| example1/web.xml:135:135 | J2EE Misconfiguration | Insecure Transport | 3.0 | 5.0 | X || example2/web.xml:150:150 | J2EE Misconfiguration | Insecure Transport | 3.0 | 5.0 | X || example3/web.xml:109:109 | J2EE Misconfiguration | Incomplete Error Handling | 3.0 | 5.0 | X || example4/web.xml:108:108 | J2EE Misconfiguration | Incomplete Error Handling | 3.0 | 5.0 | X || example5/web.xml:166:166 | J2EE Misconfiguration | Insecure Transport | 3.0 | 5.0 | X || example6/web.xml:2:2 | J2EE Misconfiguration | Excessive Session Timeout | 3.0 | 5.0 | X || example7/web.xml:162:162 | J2EE Misconfiguration | Missing Authentication Method | 3.0 | 5.0 | X |+--------------------------+-----------------------+-------------------------------+----------+------------+-------------+
输出至CSV文件:
$ sr2t --fortify example/fortify.fpr -oC example$ cat example_fortify.csv,type,subtype,severity,confidence,annotationsexample1/web.xml:135:135,J2EE Misconfiguration,Insecure Transport,3.0,5.0,Xexample2/web.xml:150:150,J2EE Misconfiguration,Insecure Transport,3.0,5.0,Xexample3/web.xml:109:109,J2EE Misconfiguration,Incomplete Error Handling,3.0,5.0,Xexample4/web.xml:108:108,J2EE Misconfiguration,Incomplete Error Handling,3.0,5.0,Xexample5/web.xml:166:166,J2EE Misconfiguration,Insecure Transport,3.0,5.0,Xexample6/web.xml:2:2,J2EE Misconfiguration,Excessive Session Timeout,3.0,5.0,Xexample7/web.xml:162:162,J2EE Misconfiguration,Missing Authentication Method,3.0,5.0,X
项目地址
sr2t:【GitLab传送门】
